A Preliminary Study on Collaborative Management of Intellectual Property in Supply Chain Enterprises | Semantic Scholar
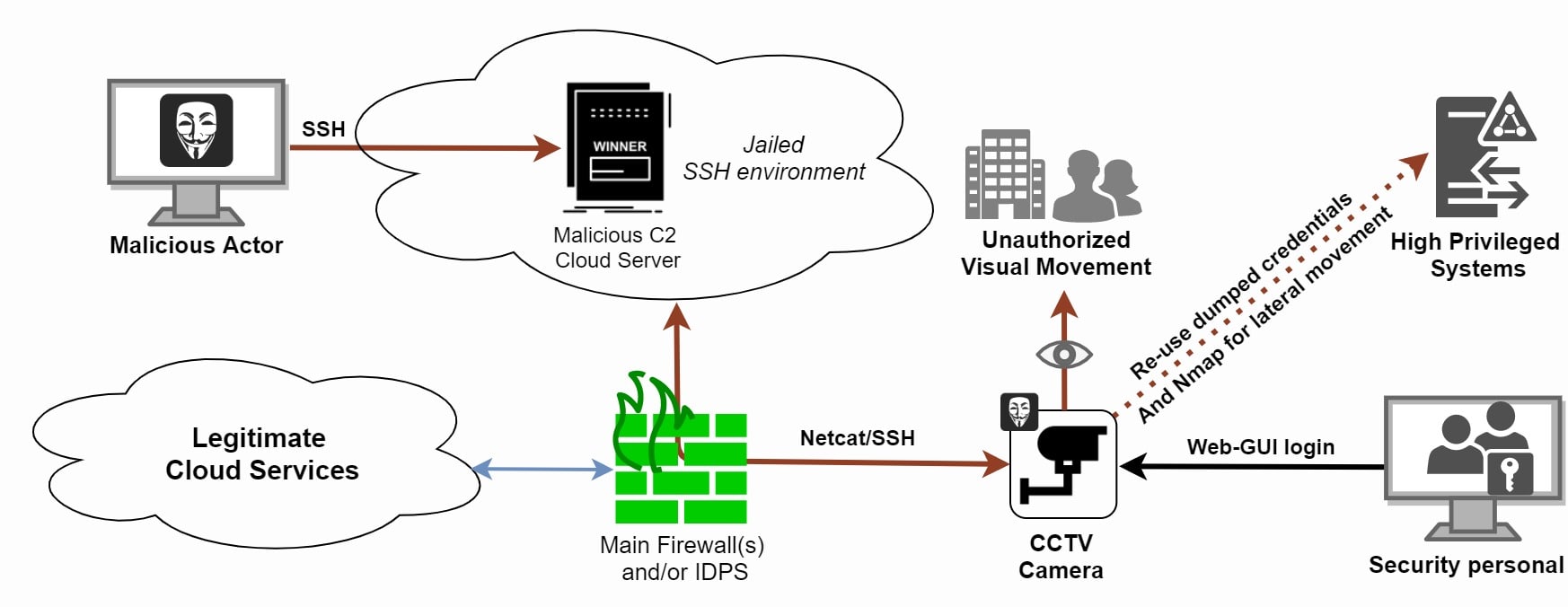
![PDF] An On-Chip Dynamically Obfuscated Wrapper for Protecting Supply Chain Against IP and IC Piracies | Semantic Scholar PDF] An On-Chip Dynamically Obfuscated Wrapper for Protecting Supply Chain Against IP and IC Piracies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f15fb6b6f4e5034b0246d3869f7a0b53b0bacdd5/3-Figure1-1.png)
PDF] An On-Chip Dynamically Obfuscated Wrapper for Protecting Supply Chain Against IP and IC Piracies | Semantic Scholar

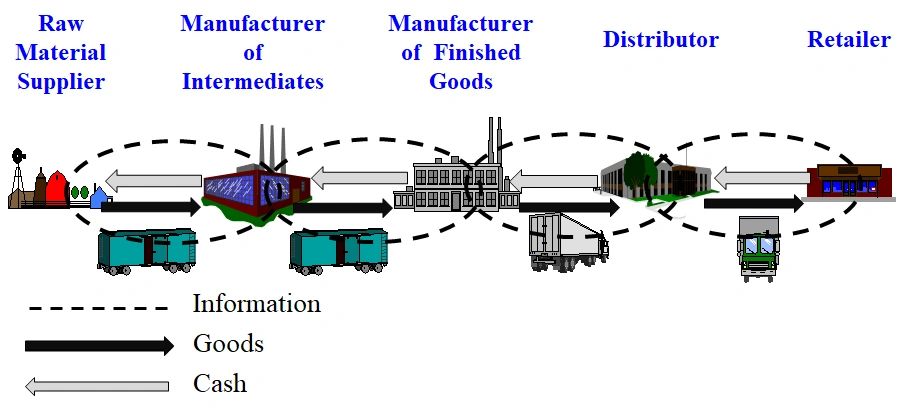
ECI Academy Batam Twitterissä: "Evolution of Supply Chain Management # supplychain #blockchainnovation https://t.co/g0xNB6EBbC" / Twitter

Protecting IP in Global Supply Chains: Tech, Policy, and Best Practices - The National Bureau of Asian Research (NBR)
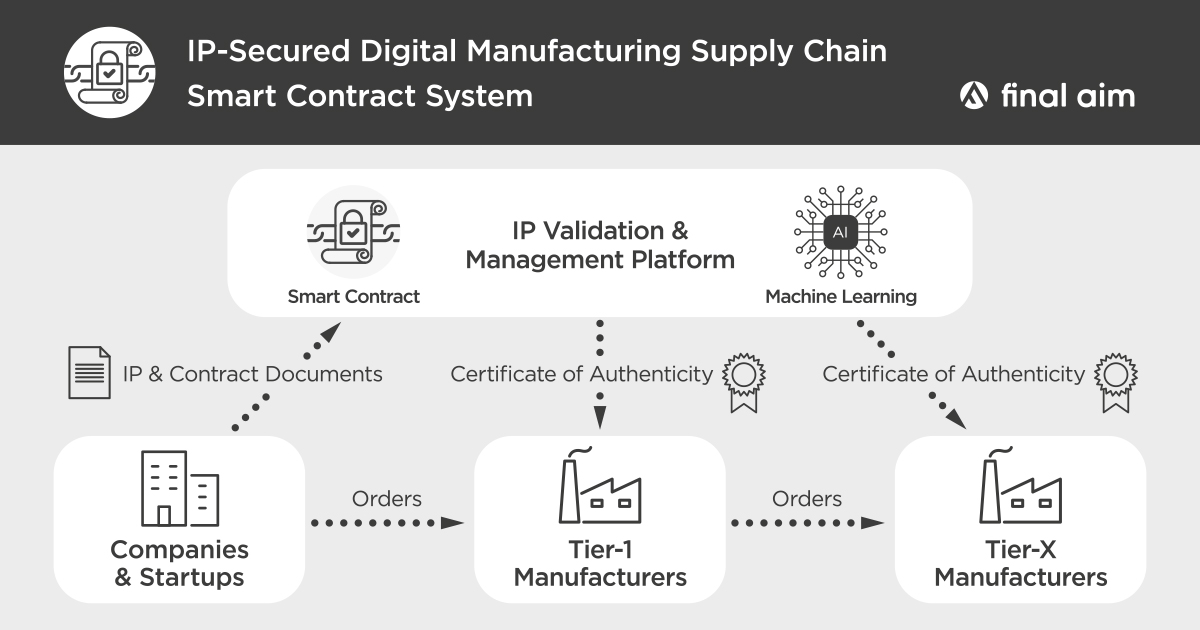
Final Aim Filed the Third Patent Application for Smart Contract in Digital Manufacturing | Final Aim Inc.

Ic Chain Supply ) CXD2813R CXK581000AP 55LL PI3B3126QX PE 62892 PE 65498 SJ8207A SIQ4532DY T1 E3 FA5508AN TE1 73K324SL IP GRM15 | AliExpress
IP Carrier: Moving up the Stack, or Across the Value Chain: Difficult, but Perhaps Not Impossible for Telcos