SolarWinds Cyber Attack: Attackers Leverage Supply Chain to Compromise Multiple Global Victims – dynamicCISO

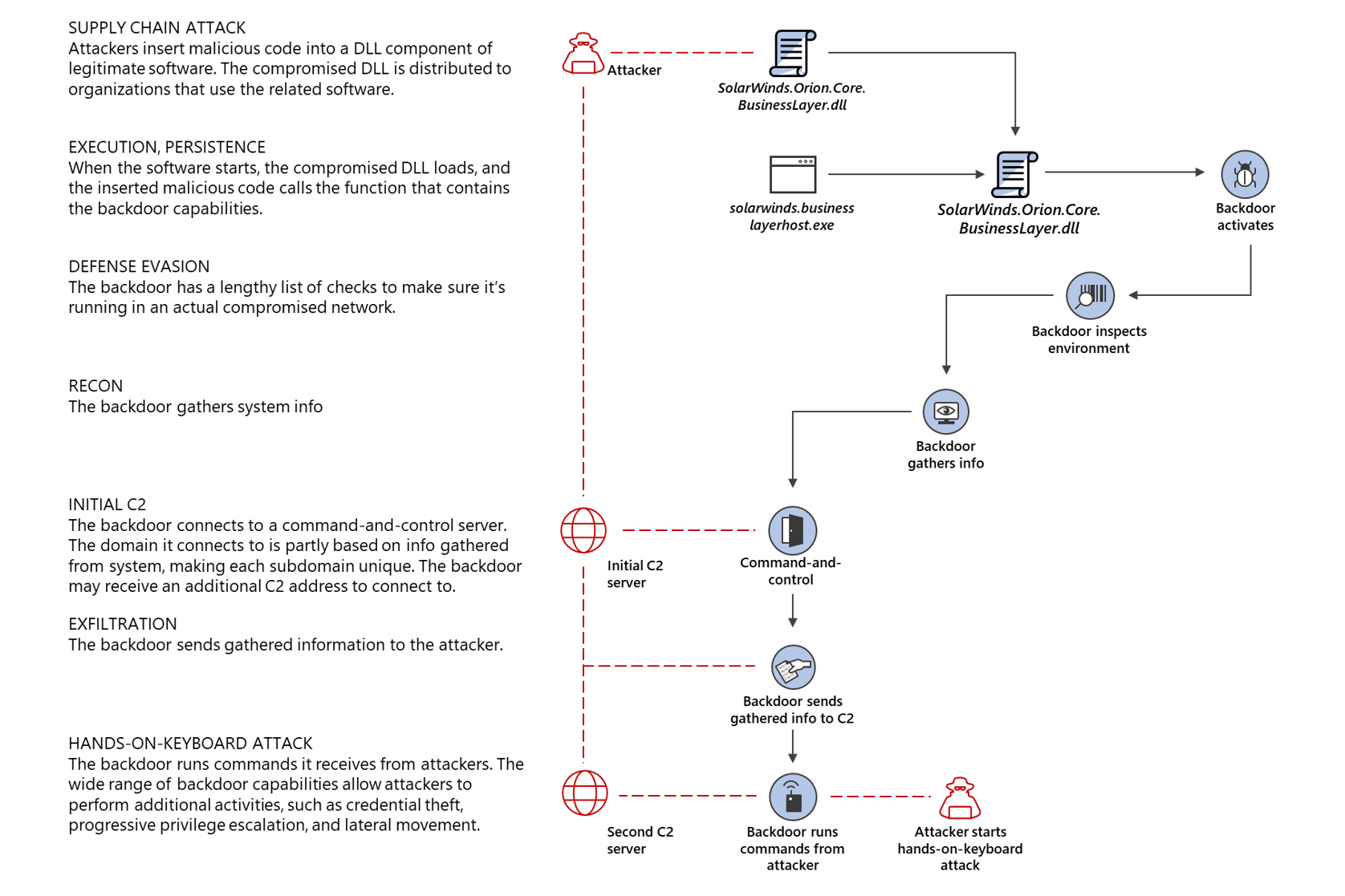
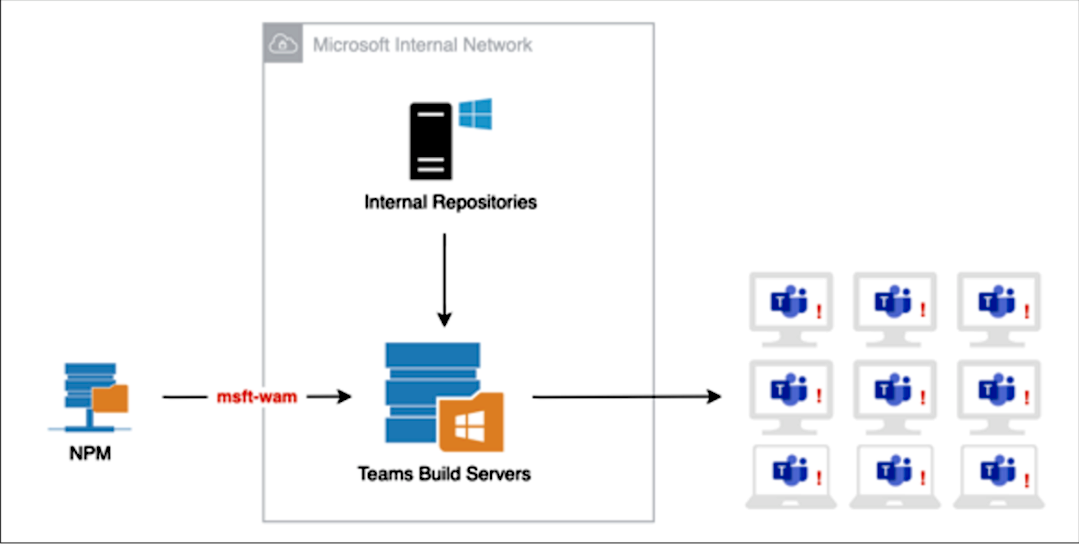
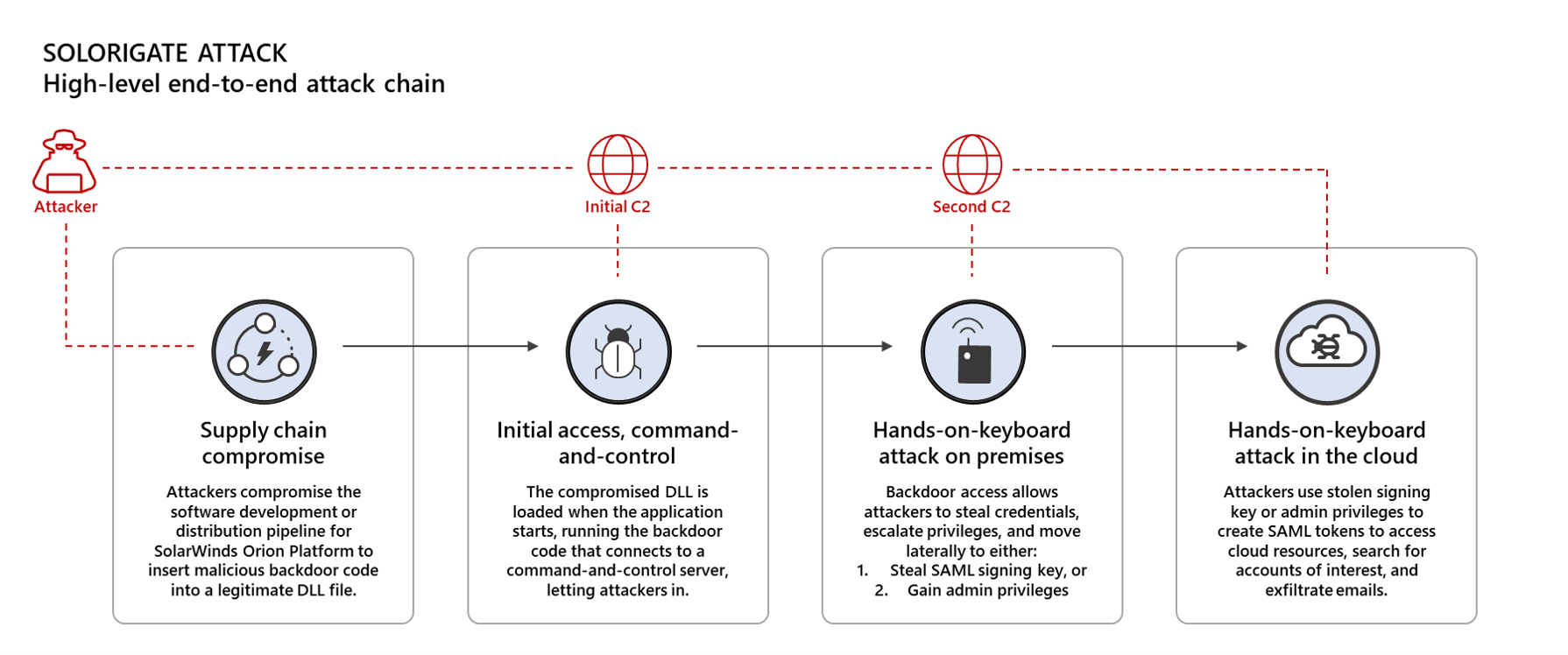
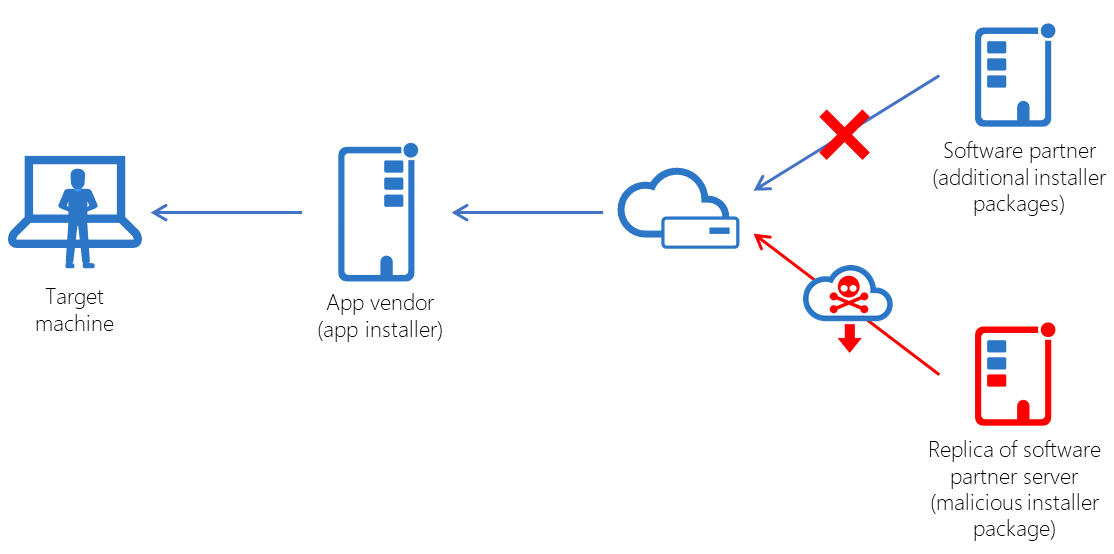
Attack inception: Compromised supply chain within a supply chain poses new risks - Microsoft Security Blog
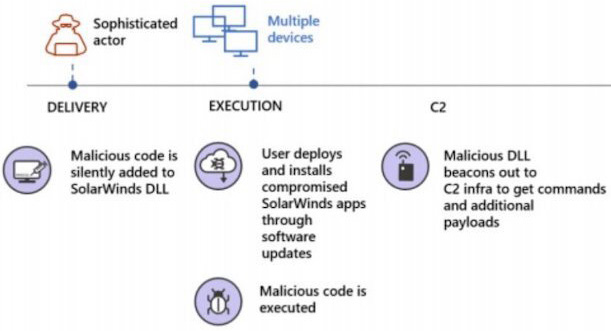
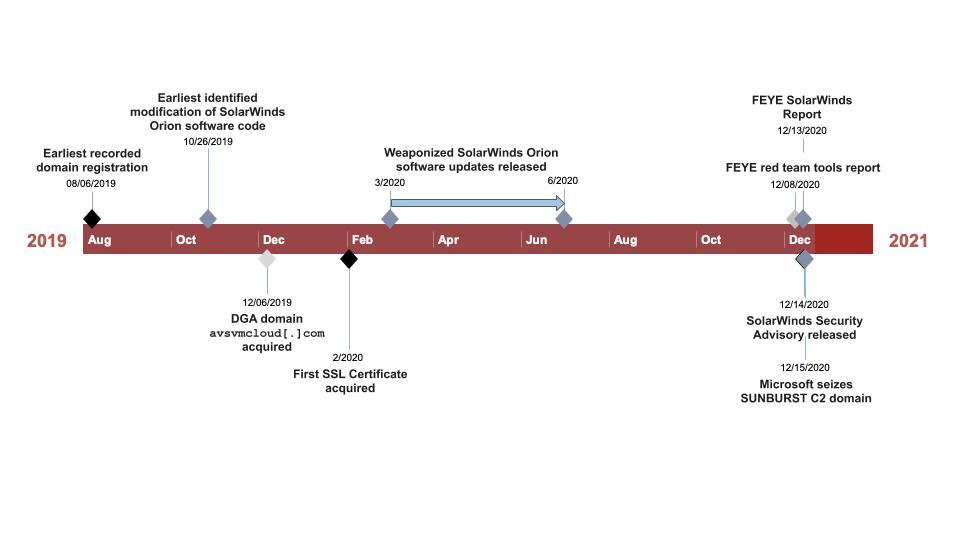
Hackers breached U.S. government agencies via compromised SolarWinds Orion software - Help Net Security

Can We Prevent the Spread of Software Supply Chain Attacks? A Retrospective of SolarWinds, Accellion FTA, and More | Penta Security Systems Inc.